Overview
The Administration Panel is the essential tool for our Partners to work with your Verestro services. The main purpose of Admin Portal is to provide a web-based environment with the ability to manage customer service actions. The presented solution is prepared for customisation with Partner's brand.
This document is divided into sections that describe the various components of the system. Each section contains a screen presenting the functionality and a detailed description of the states occurring in it.
The mechanisms described in this documentation are the most important ones for all web-based products that rely on Admin Portal. Some functionalities of Verestro have specific screens and processes that are not described here. Administration Panel is going through on-going development and changes to improve its performance so there may be differences in this description and real panel.
Purpose and scope
This product guide provides a high-level overview of Admin Panel Management. This document covers the following topics:
-
description of the all aggregates of operators, including detailed information and possible actions,
-
description of possible configurations,
-
granting access,
-
description of main processes as: login, reset password,
-
additional and optional functionalities.
Terminology
This section explains a number of key terms and concepts used in this document.
|
Name |
Description |
|
Operator |
User using the Portal regardless of role or level of rights. |
|
Session token |
Access to the system by a web application user is secured using a session token to uniquely associate the session with the user. It is required to perform any action. |
Access and configuration
Access solutions
The access to Admin Portal in available in 3 ways:
-
direct traffic through VPN (Virtual Private Network) - requires VPN reconfiguration on both sides,
-
block access to the domain and allow access from a particular IP address (specific IP addresses or a range
of addresses) - configuration required on Verestro side,
-
free access for everyone, who have an account in Admin Portal (no matter if VPN configuration or IP
address are set.
Admin Portal is available on two environments:
▪ test environment (dev/UAT environment),
▪ production environment.
Sample of test environment (URL): https://admin-panel-nameofclient.verestro.dev/
Sample of production environment (URL): https://admin-panel-nameofclient.verestro.com/
IMPORTANT: There is also option to use custom domains.
Configuration of Admin Portal
Admin Panel has a several default parameters related to the time of each action. Table below describes particular action and time of session token.
| Action | Description |
Accessibility time |
|
Reset password |
Validity of link to reset password. |
60 minutes |
|
Create an account |
Validity of link to first login to Admin Panel. |
60 minutes |
|
Login to the panel |
Validity of code (4 numbers) to login. |
10 minutes |
|
User session |
Session after successful login to the panel. |
15 minutes |
|
User lock |
Time of lock due to incorrect password. |
max 24h (until midnight next day) |
|
Registration link |
Validity of invitation link. |
60 minutes |
These are the default values, they can be changed at the request of the customer.
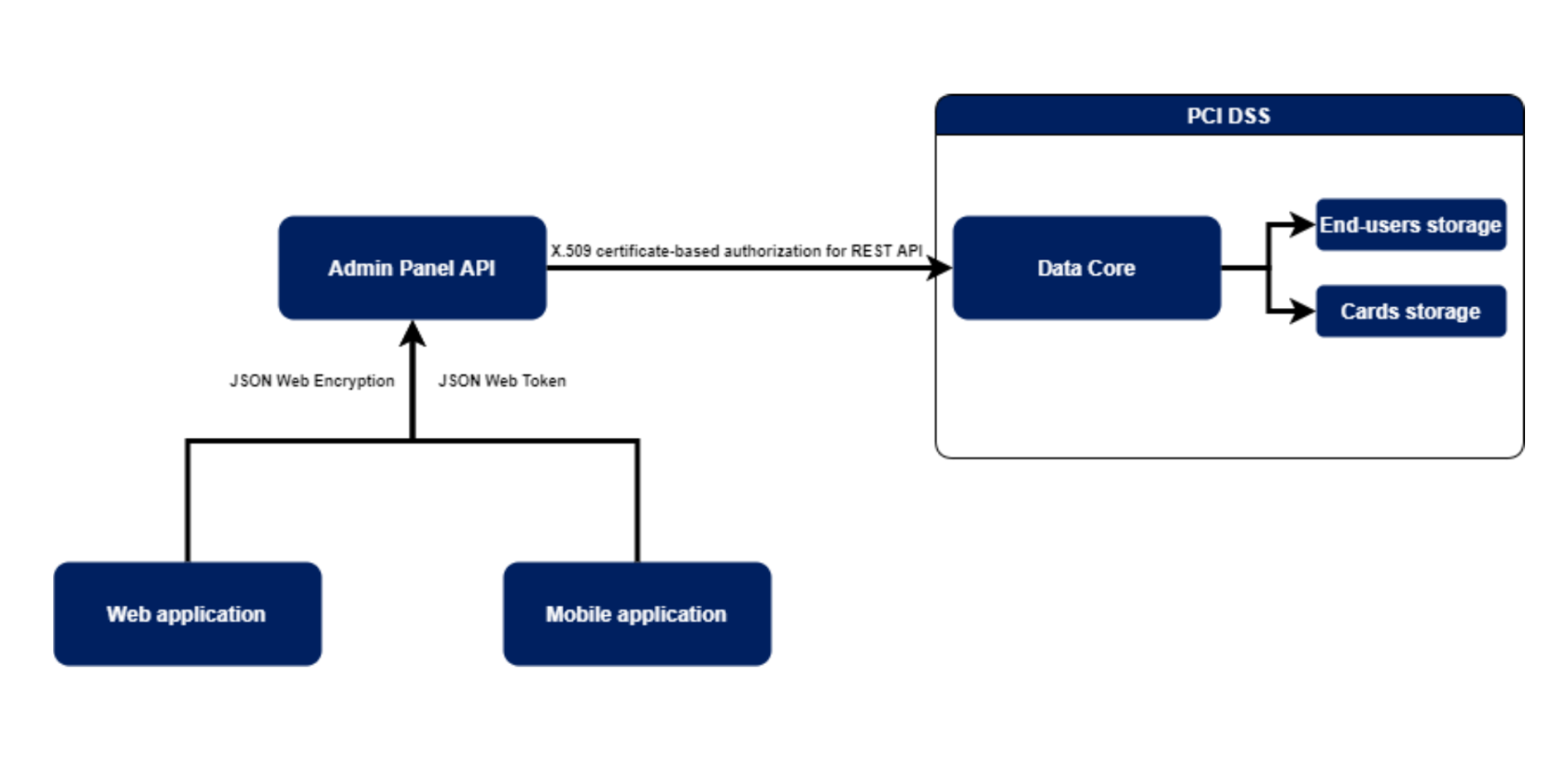
Security
The systems offered by Verestro are fully secure, which is confirmed by current third-party certificates. As we store card and payment data we are obliged to comply with strict legal requirements. Card and user data are stored in a specially designed environment - Data Core. This environment is PCI DSS certified. The PCI-DSS standard guarantees the security of payment card data. It ensures that sensitive information is properly guarded and provides maximum security in the payment process. The portal operators' passwords are kept in a different database from the end users' data for security reasons. To encrypt them the algorithm Bcrypt with a cost of 10 is used. The cost parameter specifies a key expansion iteration count as a power of two, which is an input to the crypt algorithm.
We achieve high security standards by, among other things :
-
Building and maintaining network security - the need to build and maintain a firewall configuration that protects cardholder data, not using manufacturers' default passwords and settings.
-
Protecting cardholder data - protecting stored cardholder data, encrypting data transmissions when using public networks.
-
Maintaining a payment management program - using regularly updated anti-virus systems, developing secure systems and applications.
-
Implementing strong access control methods - limiting access to cardholder data to only those with a business need, assigning each user a unique ID, limiting physical access to cardholder data.
-
Regular network monitoring and testing - testing security systems and processes, controlling access to network resources and cardholder data.
-
Maintaining information security policies - relying on security policies for employees and vendors.
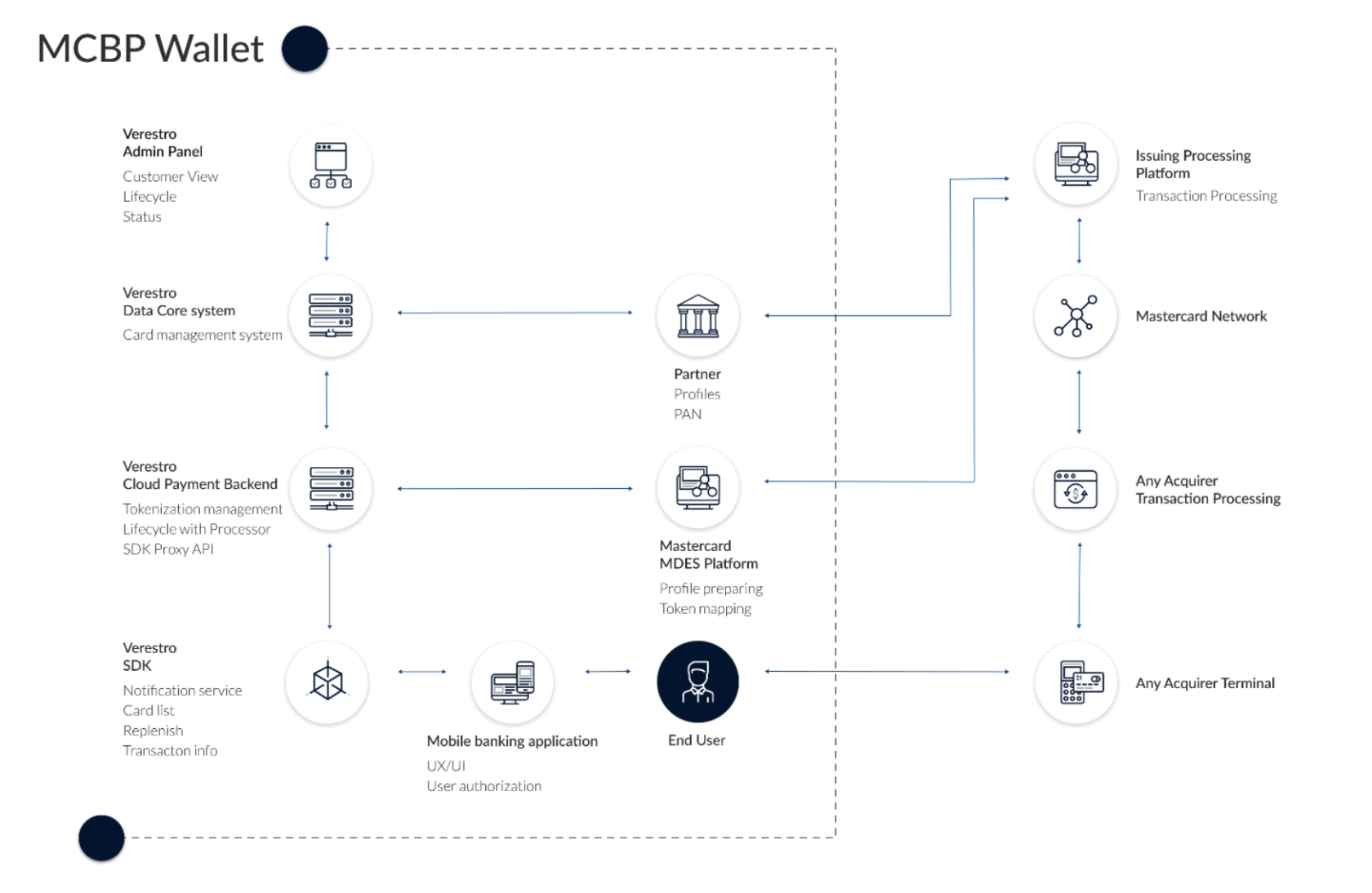
Architecture
Admin Panel uses Verestro's distributed systems to provide the highest quality of service. It is practically the best architectural solution these days. As mentioned in the previous chapter, the communication between services is completely secure, maintaining the highest security standards. This kind of system guarantees not only high efficiency, due to the division of responsibilities between the components, but also allows for easy and fast scaling of the system according to the customer's requirements.
Below is a sample architecture for the product VCP or in other words Admin Panel MDES along with MCBP Wallet.
Login procedure
First login (activation)
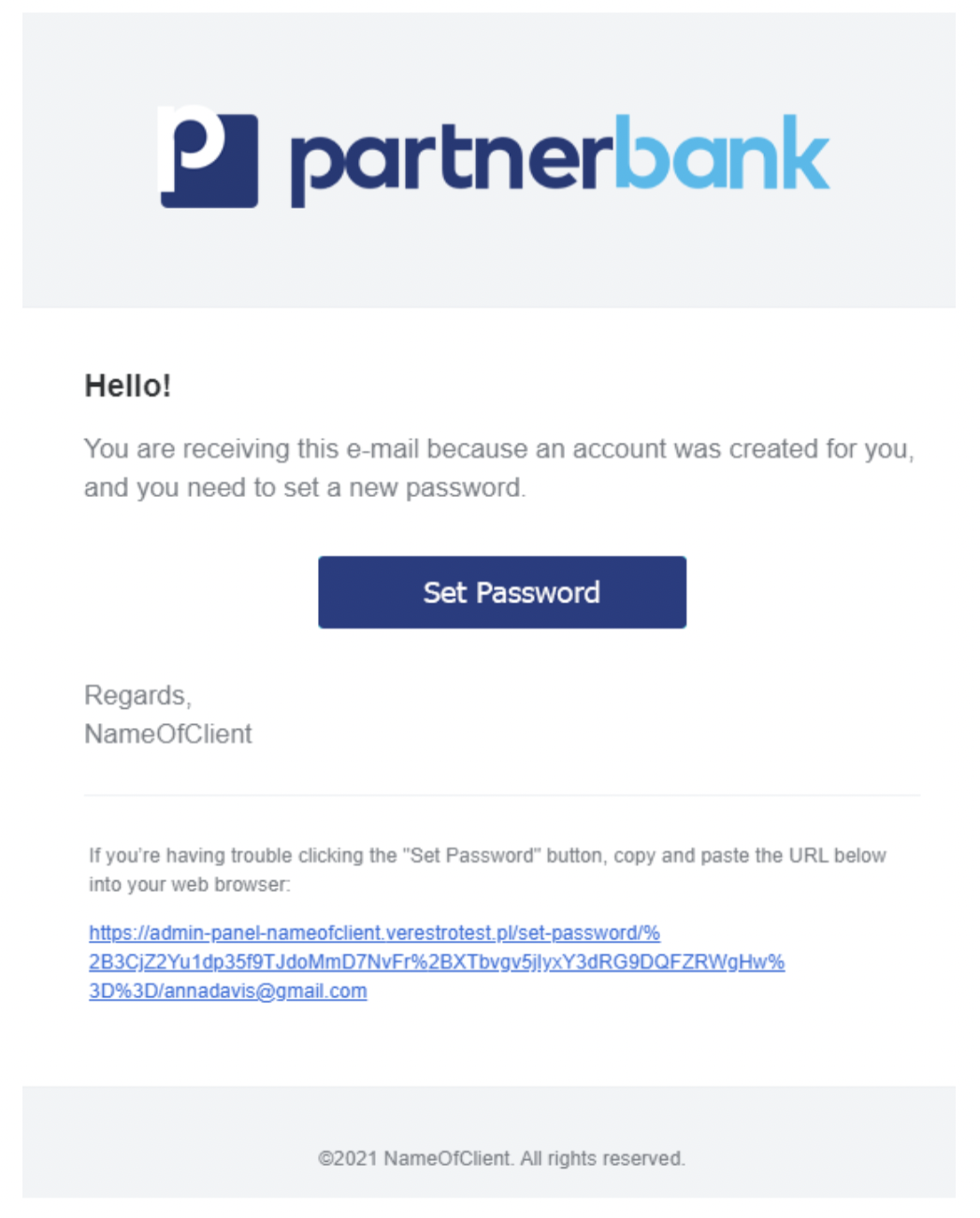
Users could be added only from the panel. It is not possible to register in the system without an invitation. Basic administrators accounts that can be used to create a user hierarchy are provided with the panel instance.
In order to create a new user account you have to log in to the panel using your e-mail address, which is user login. Then go to the "Administrators" tab and fill in the required data. After filling in the role, personal data and e-mail address there will be sent a welcome message with an activation link for new account.
Once the email send process is complete, the invited user will receive a message. It contains a welcome and an activation link - used to set a password to access the system.
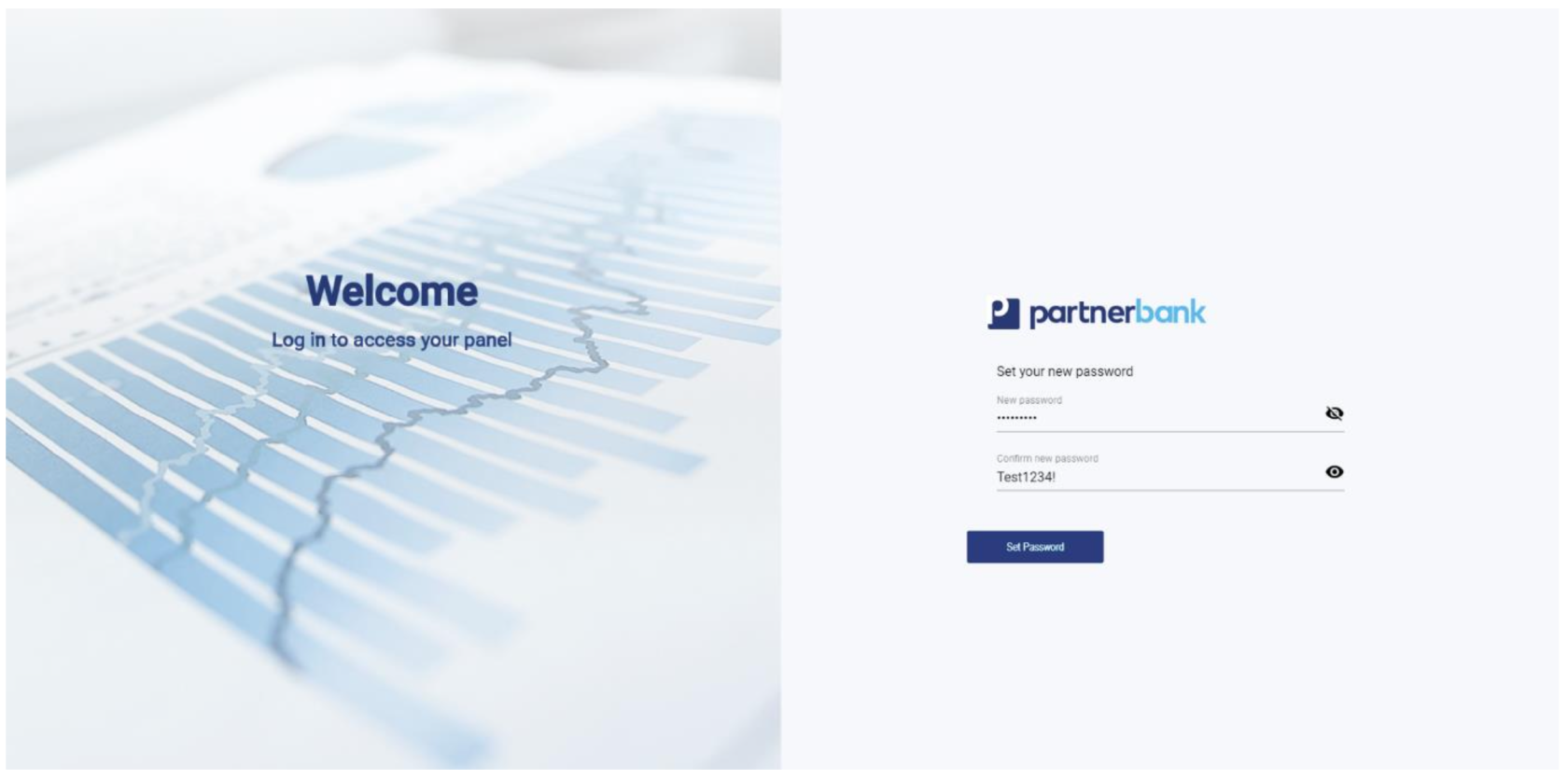
Clicking on the link redirects to the login page, where the employee will have to set a password during the first logging in. The required password standard is a minimum of 8 characters, at least one digit, one capital letter and one letter.
Login procedure
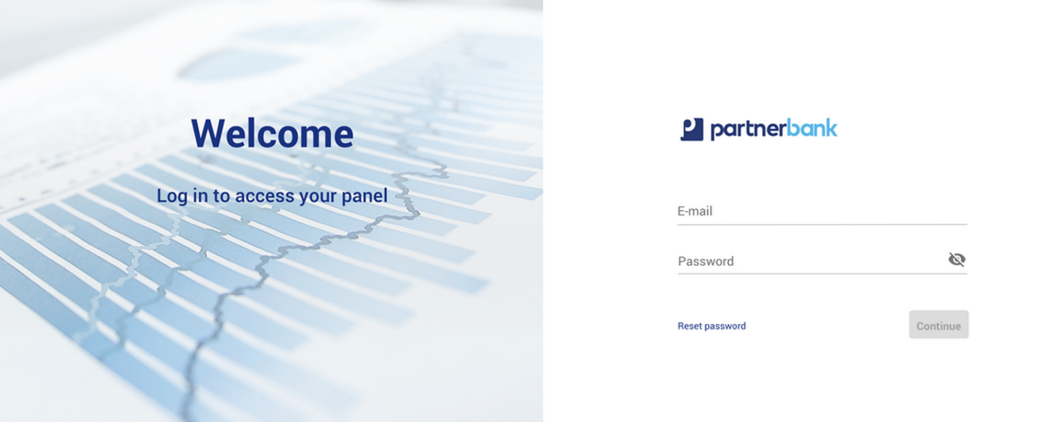
Operator must provide correct pair – e-mail and password. If the provided login is incorrect, a message informing the employee of an error “Incorrect e-mail or password” and the possibility of another attempt will be displayed.
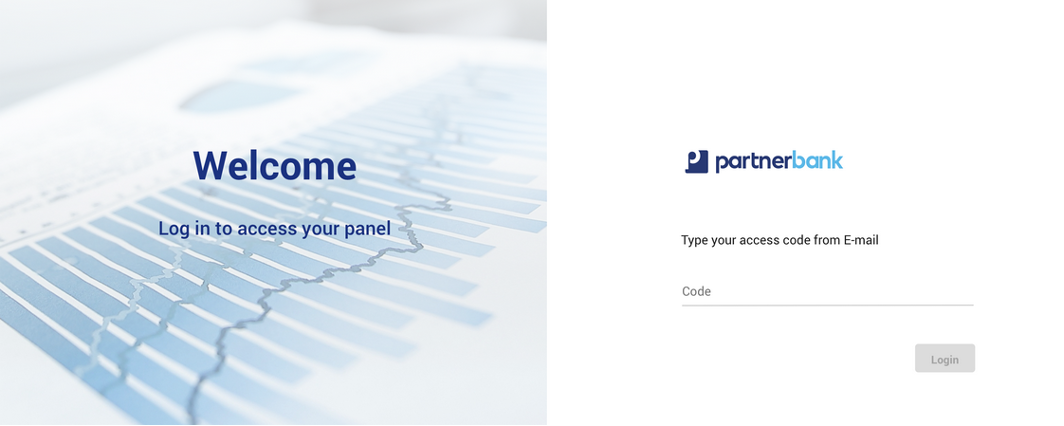
If the data provided is correct, an authentication code is sent. This is required to complete the next step of the two-step login.
As last step application asks for code. Sent code has set validity time. If code will not be provided in this time, login procedure must be started from first step.
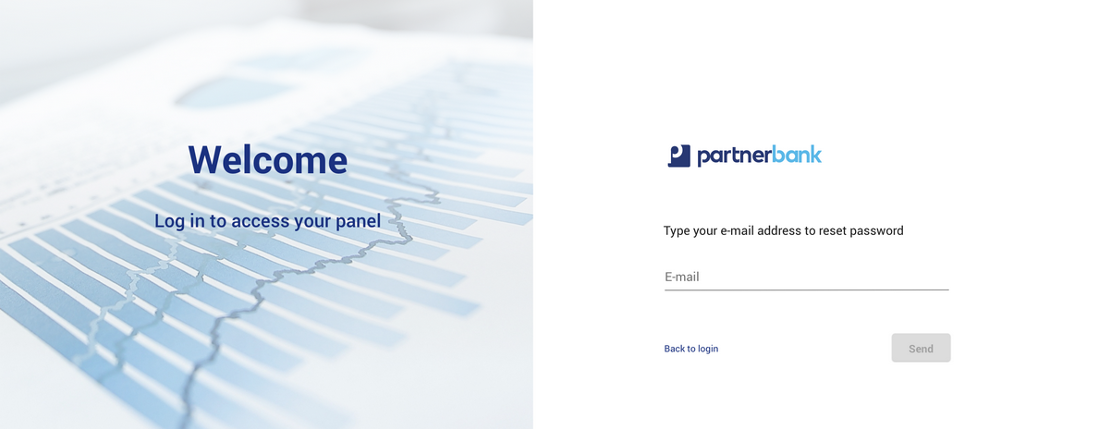
Reset password procedure
In order to reset password, admin has to open the login page and click option “reset password” (located under e-mail and password inputs). In next step, admin must provide correct e-mail address.
If the provided e-mail is correct, reset password link will be send to the employee's company e-mail address.
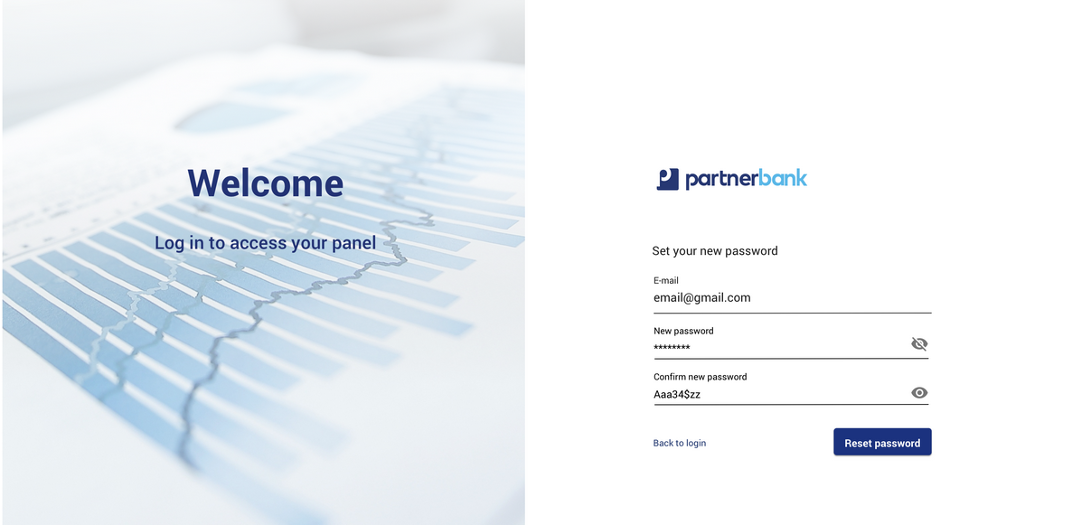
Clicking on the link redirects to the reset password page, where the employee will have to provide his e-mail address and set a new password. The required password standard is a minimum of 8 characters, at least one digit, one capital letter and one small letter.
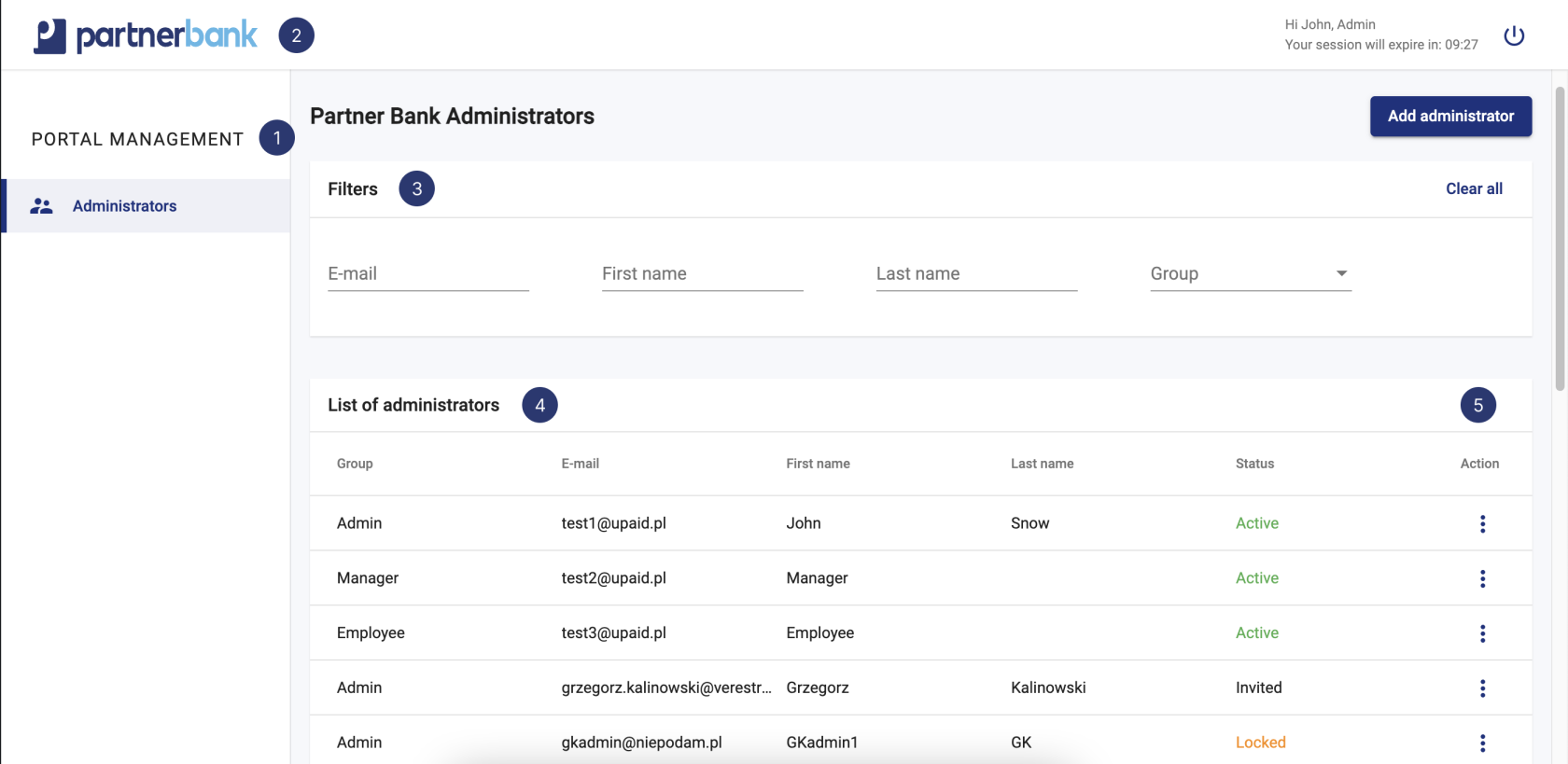
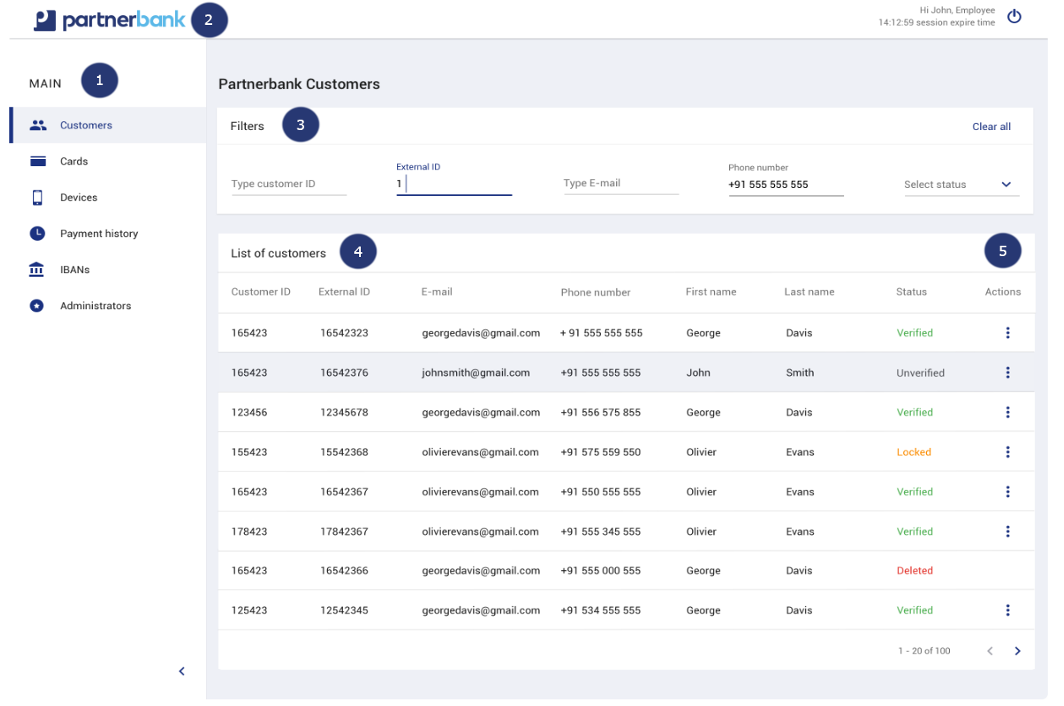
Main view
Once the authentication process is properly completed, the bank employee has access to the panel. He is shown the main screen of the system. Depending on the assigned rights group its appearance may vary. Different roles in the system have different tabs available.
The components that make up the Admin Portal are:
1) Main menu contains aggregates as: customers, cards, devices, payment history, IBANs, project administration (administrators, visuals, logs).
2) Admin Panel adjusted to the client’s colours and logotype.
3) Filters allows to select multiple filter options and display results that contain information all the selected criteria.
4) List of the most important information referring to each aggregate (example: customers).
5) Actions allows admin to change the status of aggregate or edit data.
Operator administration
Roles and permissions
From the perspective of the bank’s operations team or call center staff, access to authorization levels is now managed using access labels rather than 3 predefined roles as it was in the past.
Three standard access labels have been introduced to reflect the typical organizational hierarchy:
-
employee -
manager -
admin
These labels correspond to different access levels and responsibilities related to operational functionalities within the portal. The core duties available under each label include customer verification, data visibility, and in some cases, data editing.
On request, we can create additional privilege levels such as readonly or privileges for level 1 support and level 2 support.
Operators may hold one or more labels simultaneously, allowing for flexible and precise permission management tailored to the needs of the institution.
|
Aggregate area |
Action |
Admin |
Manager |
Employee |
| Portal management - Operators | View | x | x | - |
| Create | x | x | - | |
| Edit | x | x | - | |
| Delete | x | x | - | |
| Lock | x | x | - | |
| Unlock | x | x | - |
-
An operator with the
adminlabel:-
Can view, create, edit, and delete other operators, regardless of their assigned labels.
-
Has full visibility of all users, including other
admin,manager, andemployeeoperators. -
May assign any access label to other operators.
- Has access to access label management (assign to operator).
-
-
An operator with the
managerlabel:-
Can manage operators labeled as
employeeonly. -
Has access to operator management functions (view, create, edit, delete) within this scope.
-
Cannot view or modify users with
manageroradminlabels.
-
-
An operator with the
employeelabel:-
Does not have access to operator management functionalities.
-
Can only perform tasks allowed within their assigned label scope, as defined per product configuration.
-
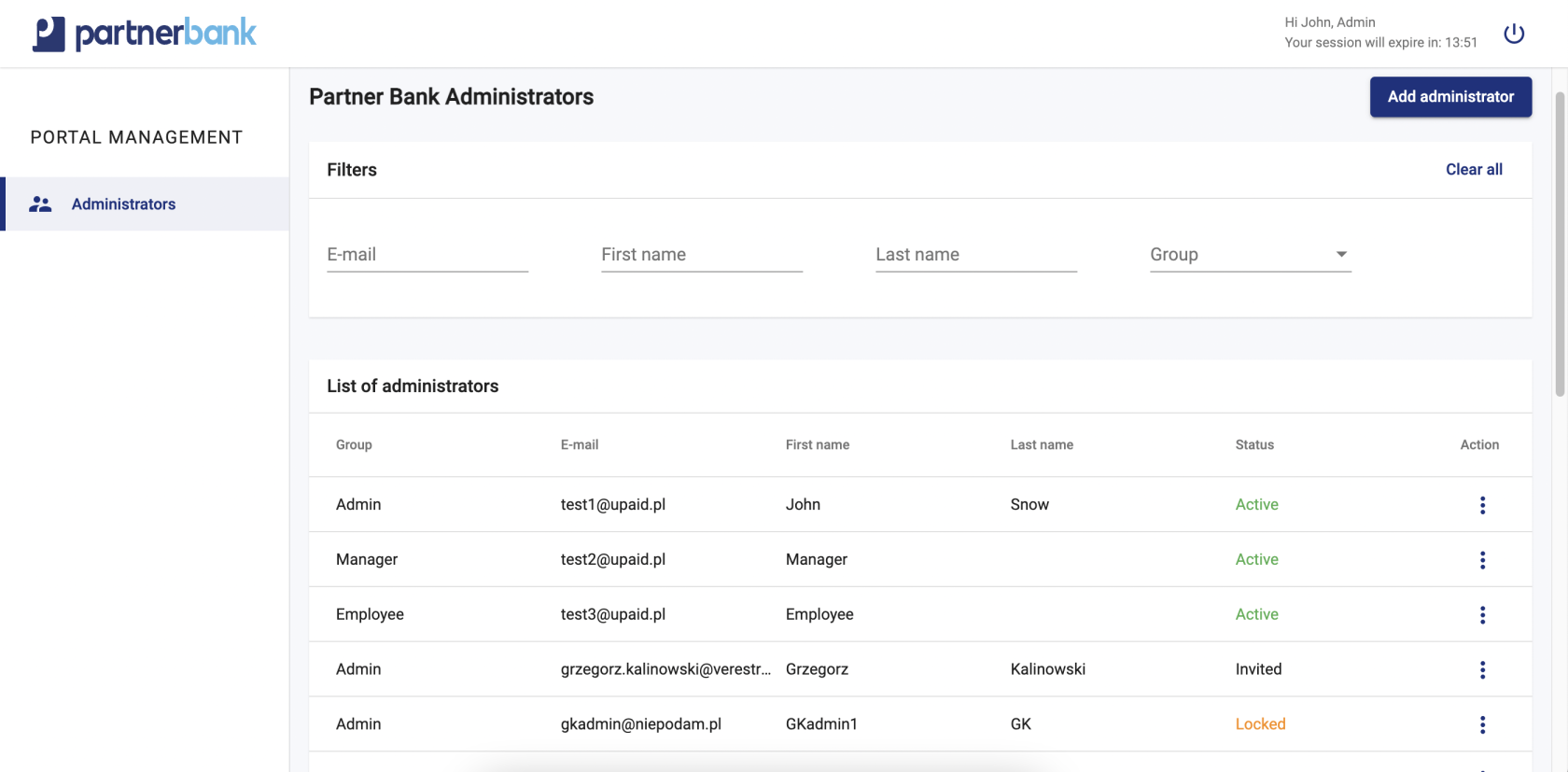
Operators list
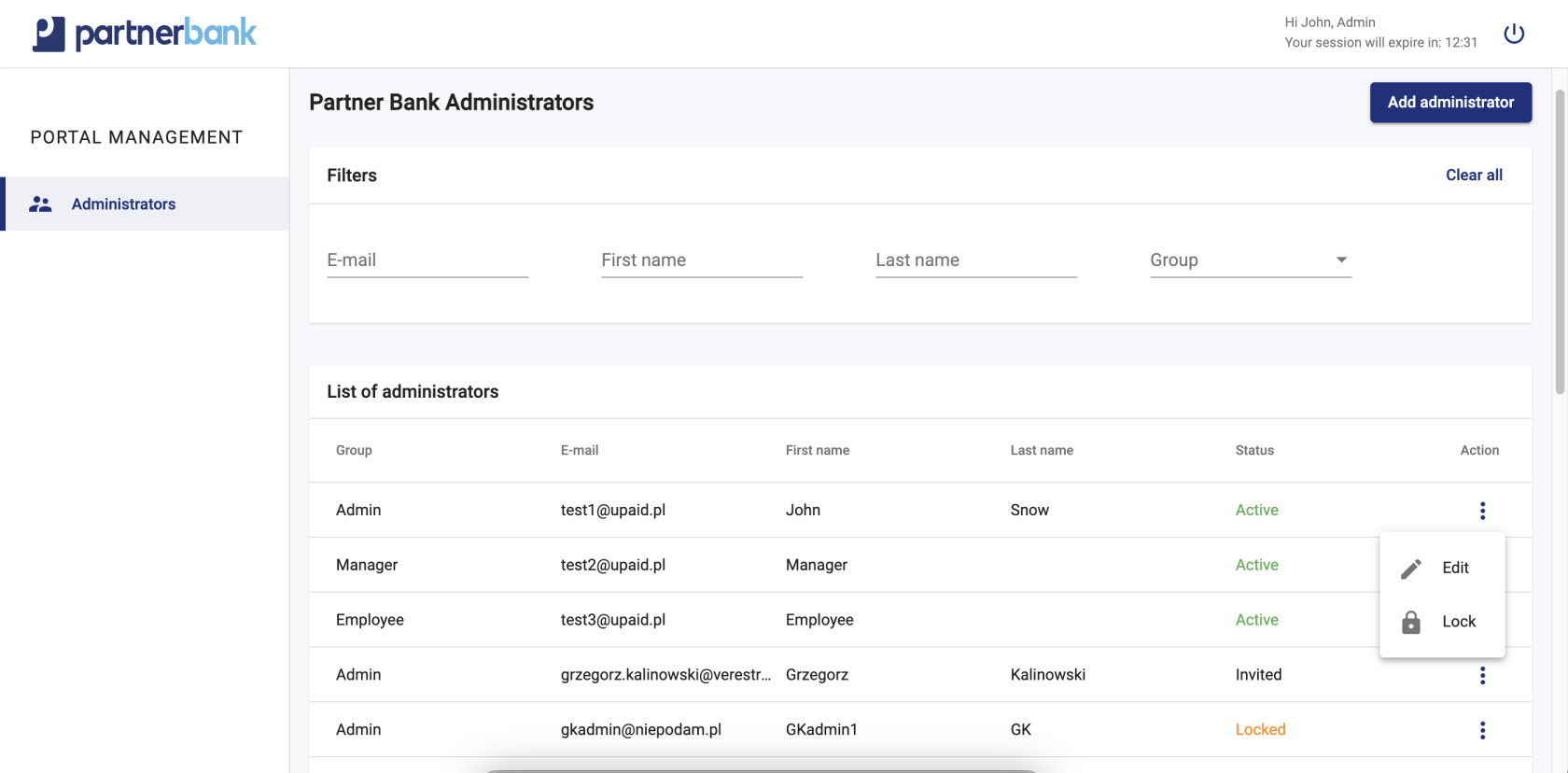
Administration Panel Accounts list contains filters and columns with dates. In this section detailed lists don’t occur. The filters are used for dynamic searching, such data as: e-mail, first name, last name, group (available: admin, manager, employee).
Basic list includes following information:
|
Parameter |
Description |
|
Group |
Group determines the access level. |
|
|
Admin e-mail address. |
|
First name |
Admin first name. |
|
Last name |
Admin last name. |
|
Status |
Admin status (described in admin statuses part). |
|
Actions |
Action which can be performed on particular admin (described in admin actions part). |
Account statuses
|
Name of status |
Description |
| Inactive | The inactive status means that the operator account was created with the is_active=false flag. No invitation has been sent to the system. This is an optional status. |
| Invited | The invited status means that the invitation to the system (password setting link) has been sent to the operator. This is possible in two cases: 1. the account was created with the flag is_active=true. 2. the account was created with the flag is_active=false and then activated. |
| Active |
The active status means that the operator has properly completed the registration and activation process, i.e. has created a password to the portal (using the link with the invitation or the resetPassword procedure if the link has expired). In this status the access to the portal is possible - it is the only status that allows a proper login. |
| Locked |
The locked status clearly indicates that the operator has been locked by another operator. This status can be applied to all statuses except deleted. From locked status operator can return to his previous status. Moreover, if an operator with status invited has been moved to locked status and in the meantime has completed registration, then after removing the lock it will have active status - not invited as it was before the lock. |
| Deleted | The deleted status means that the portal operator has been irreversibly removed from the system. It is not possible to restore an operator account from this status. |
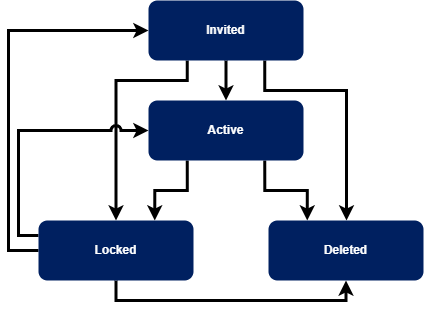
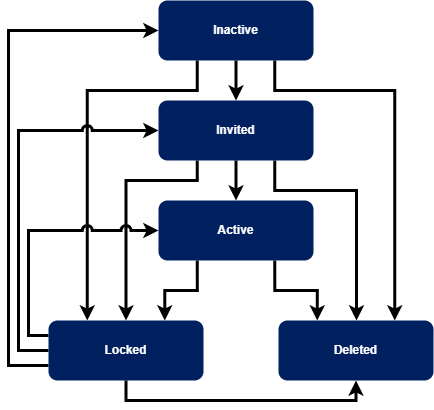
Referring to the above tables, the possible transition of operator states is presented in the diagram below.
Standard flow - operator is created in status invited (Admin Panel MDES/VCP scenario).
Alternative flow - operator is created in status inactive.
Accounts actions
Administration Panel user can perform the following actions for the particular user (admin, manager, employee):
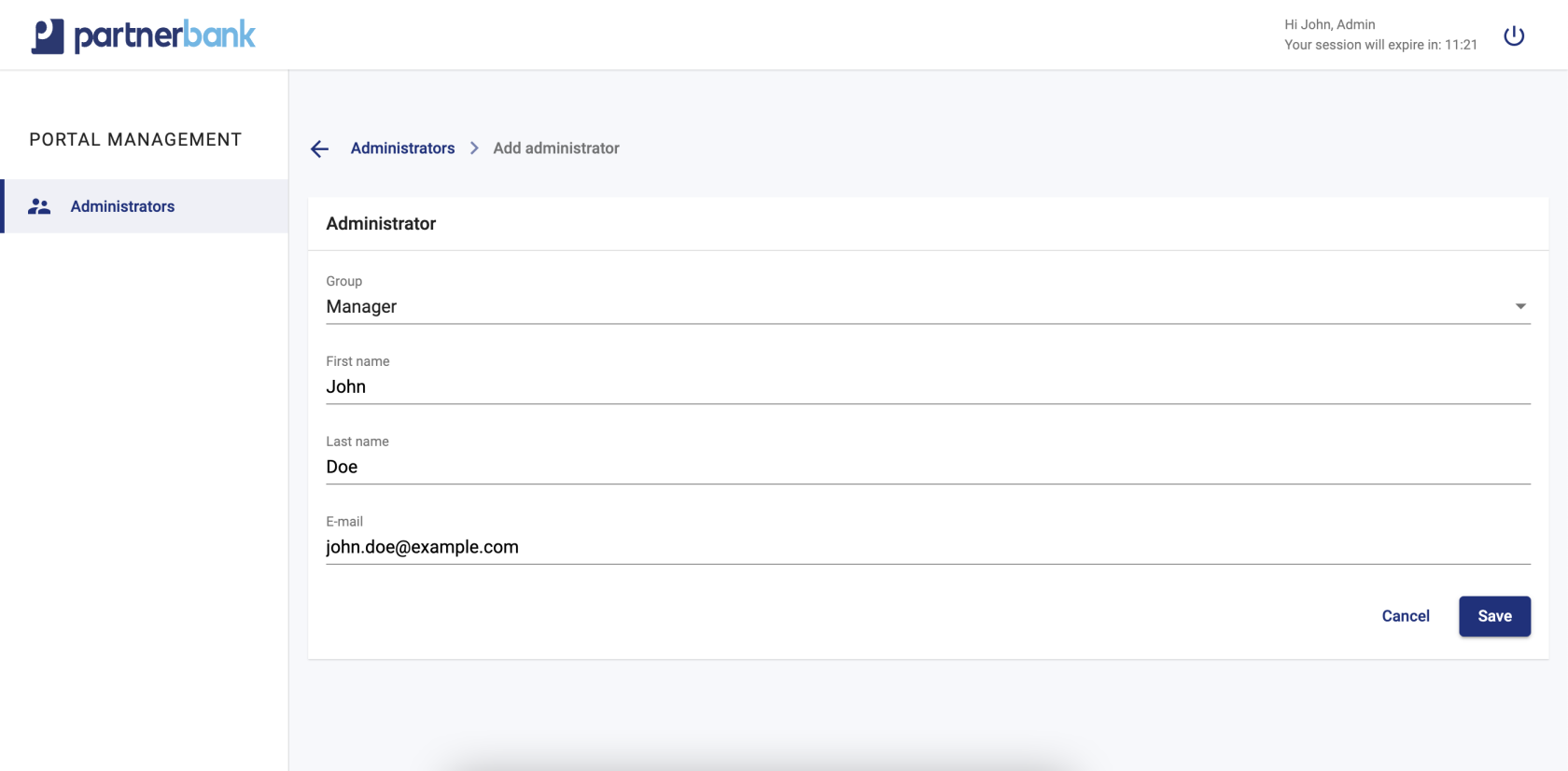
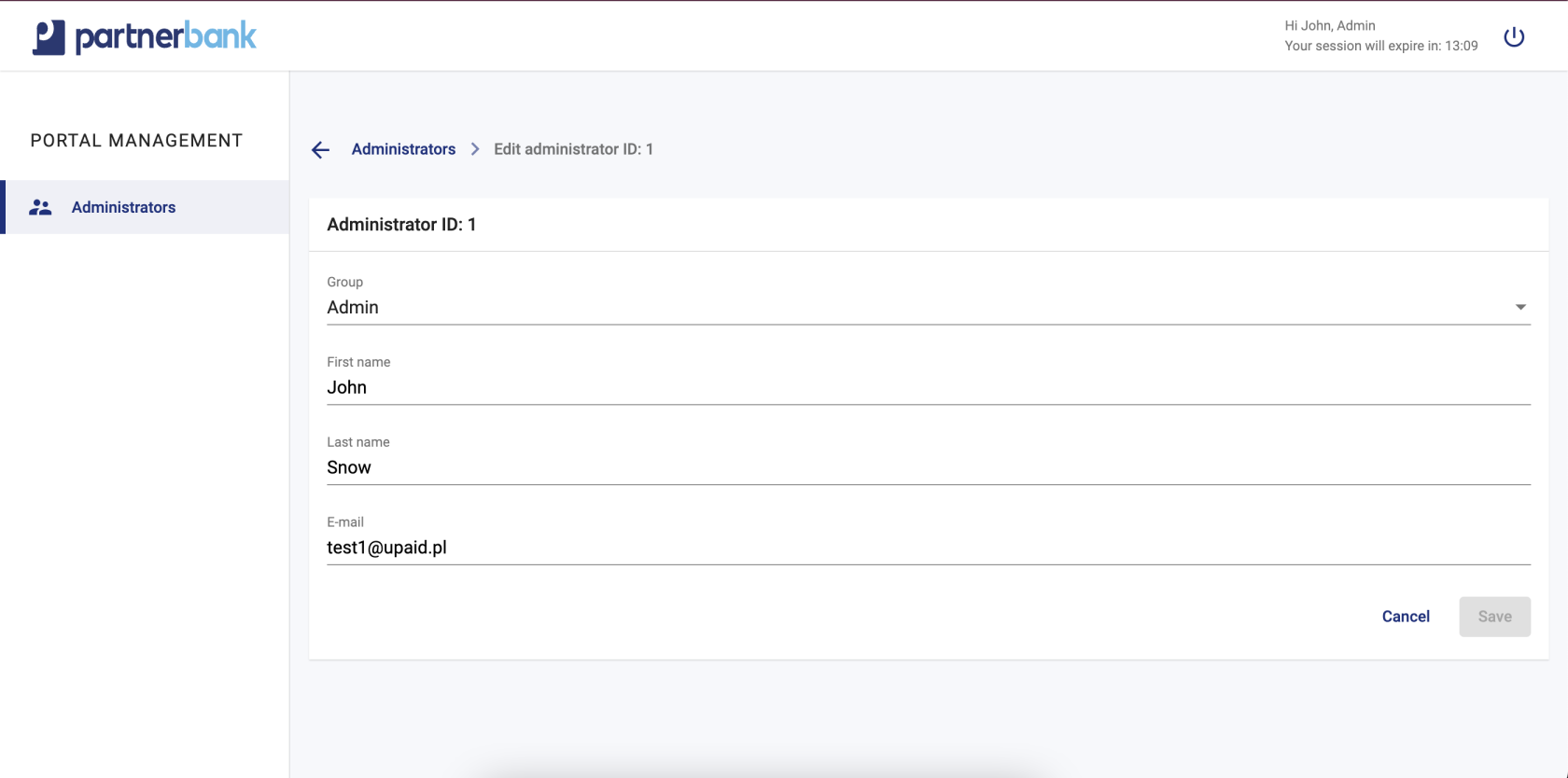
a) add admin/manager/employee – necessary to input following data: group (select: admin, manager, employee), first name, last name, e-mail. In order to confirm “Save” button should be clicked. Added user should receive e-mail with link to activate account and set the password.
b) edit admin/manager/employee – possible to change following data: group (select: admin, manager, employee), first name, last name, e-mail. There's no option to edit operator with status "invited", in this particular case it's necessary to delete invitation and add a new operator.
c) lock admin/manager/employee – temporary lock of user.
Notifications in the system
This section contains all email messages that are sent in the system to the portal operator.
Emails from Admin Panel to operator.
|
Process |
Topic |
Details |
Comment |
|
Invitation to the system |
Set password to administration panel. |
Hello! You are receiving this e-mail because an account was created for you, and you need to set a new password. <button to set password> Regards, < NameOfClient > |
Standard email sent when portal operator added new operator. |
|
Login process |
Login code. |
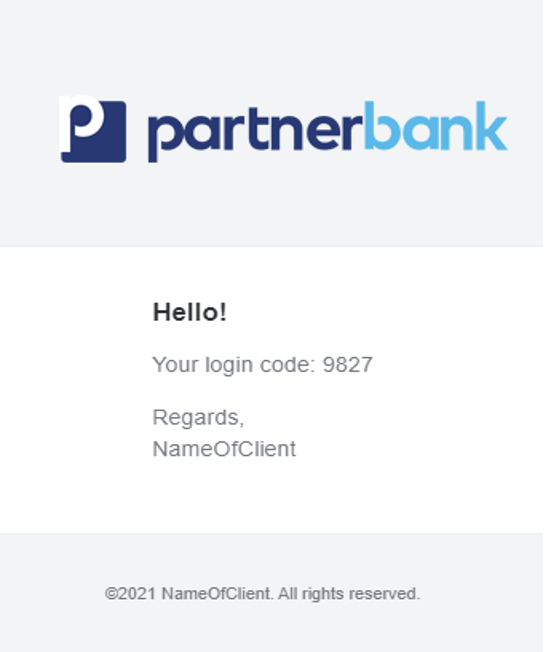
Hello! Your login code: <code> Regards, < NameOfClient > |
Standard AP email sent when portal operator entered correct email and password. |
|
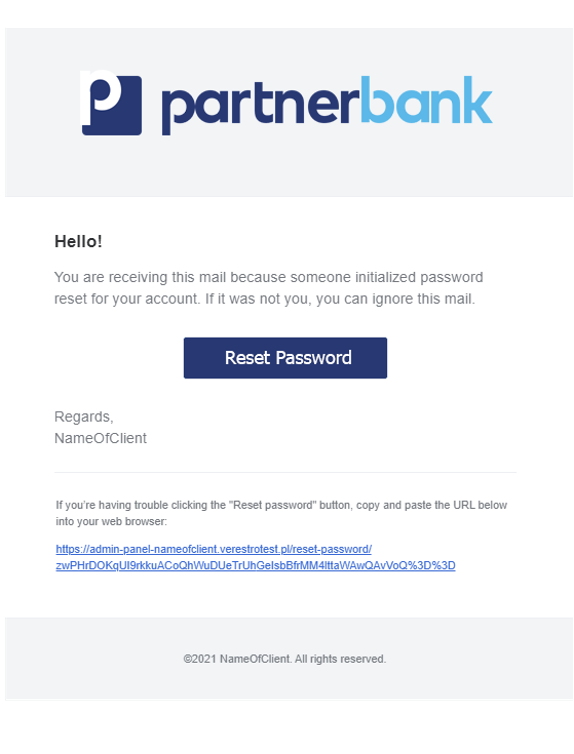
Reset password |
Reset password to administration panel. |
Hello! You are receiving this mail because someone initialized password reset for your account. If it was not you, you can ignore this mail. <button to reset password> Regards, <NameOfClient> |
Standard Admin Panel email sent when portal operator uses "reset password" button on login page. |
|
Additional password policy |
Password expiration reminder. |
Hello! Your password will expire in <NumerOfDays> days. Please change your password to avoid losing access to the portal. Regards, <NameOfClient> |
Related to additional policy to force password changes. |
|
Inactive account policy |
Inactive account reminder. |
Hello! Due to inactivity your account will be blocked in <NumerOfDays> days. Please log into the portal to avoid losing access to the portal. Regards, <NameOfClient> |
Related to the additional policy of automatically deactivating unused accounts. |
Additional features
This section focuses on additional functionality in the system. By default they are disabled, they can be enabled upon request during panel creation or panel version upgrade.
Token blacklisting
For better security, a mechanism for blacklisting session tokens has been prepared. This makes it possible to prevent unauthorized access to the portal and data using the session token of a logged out user (if the token life has not expired yet).
It should be noted that during the logout process the session token in the user's browser is destroyed, regardless of whether the blacklisting mechanism is enabled. Also, closing the browser deletes the token.
However, a theoretical scenario is that the user's token is intercepted and used for unauthorized access to the system. Access possible for the lifetime of the token.
When this mechanism is enabled, the token is blacklisted (and therefore prevented from further use despite the active life time) and each query to the backend (API Admin Panel) checks whether the token used by the user is not blacklisted.
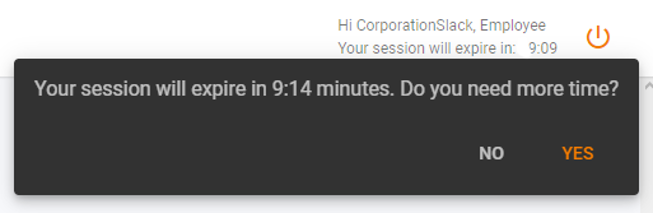
Session extension popup
Sometimes the session time may not be sufficient to perform the portal user's operations. For this reason a mechanism has been created to ask the user if there is a need to extend the current session.
It should be noted that by default when half of the session time elapses and the user performs some action (moves to another tab, clicks a button) the session time is renewed. By session time renewal it is meant that a new session token is assigned to the user and the session time counter is restored to its default, maximum value.
When the mechanism is active at a certain time before the end of the session the user is asked if he needs more time (screen below). If user chooses affirmative answer, there is assigned a new session token and the session time is restored to the default, maximum. Selecting no closes the dialog. Not selecting an option will close the dialog when the session time expires and the user is logged out.
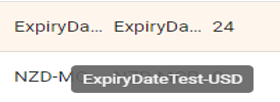
Tooltip for table row values
Depending on the resolution and screen size, the appearance of each screen may vary cosmetically. Admin Panel is responsive but values in tables can be of different length (up to 255 characters). It is not always possible to display the entire value in a single table cell. For this reason, a mechanism was created to display a tooltip for table cell values.
The default mechanism is to show the user as many characters as fit into the table cell - depending on the screen size of the device. It is possible in this case to copy the whole, valid value of the cell. Unfortunately it is not possible to preview it by user in simple way - it is necessary to copy cell value e.g. to text document to know its characters that do not fit in the cell.
By enabling described mechanism the tooltip is displayed when the user hovers the mouse over a particular value in the table and waits for 1 second without moving the mouse. The user can easily see the entire value of such a variable.
Password policies
As it is extremely important for us to ensure the security of the portal operators' data and the data to which the operators have direct access, we are providing an additional policies for passwords.
User lock
For added security, a popular mechanism has been implemented to lock the user's account for the period set in the configuration options. By default, the operator's account is blocked until the end of the day after 3 incorrect login attempts, i.e. if the user enters the wrong password 3 times, he will not log in. Such a user can be unblocked, for example, by correctly performing a password reset.
Force password change
The first of the additional policies that can be used on the admin instance of the panel is to force the operators to change the password every specified number of days. In the case of inactivity on the part of the operator the account is locked - its unlocking is possible through a password reset mechanism. Before the account is blocked, an email notification is sent about the need to change the password - the time when the email is to be sent is configurable.
Force unique password
A second, additional safeguard in password security policies is to prevent a user from setting a password that they have already used in the past. With this mechanism, it is possible to configure how many previous passwords should be excluded from reuse. Of course, for data security reasons, previously used passwords are not stored but only their unique hash, which is used for uniqueness comparison.
Deactivate inactive accounts
In order to ensure the safety of the data contained on the portal, an automatic deactivation mechanism for unused accounts has been created. It allows to define the time without logging in after which the operator will be blocked. Unblocking the account is possible by using the password reset mechanism, which is tantamount to confirming your identity and access to your e-mail address.
Handling an unavailable service
As Admin Panel consists of multiple services (as a reminder, individual services are responsible for the corresponding sections in the side menu), it is important to ensure the availability of the application when any of the individual components is not working (for example, due to a scheduled maintenance outage). For this reason, a mechanism for graying out unavailable services in the side menu has been implemented and enabled by default. If any product/service is temporarily unavailable, the portal operator can still use the functionality provided by the other services. In the case that the unavailable service becomes operational, the section becomes available again after refreshing the page.